I am releasing code to help attackers patch their binaries on the fly to avoid checksum-based detections. As I mentioned in a previous article, https://penconsultants.com/traditional-iocs-suck/, checksum-based detections are close to worthless. But, they are still used by AV vendors, intel feeds, proxy and endpoint-based detections, etc. Defenders need to stop relying on checksum-based detections. I’m releasing […]
Month: October 2017
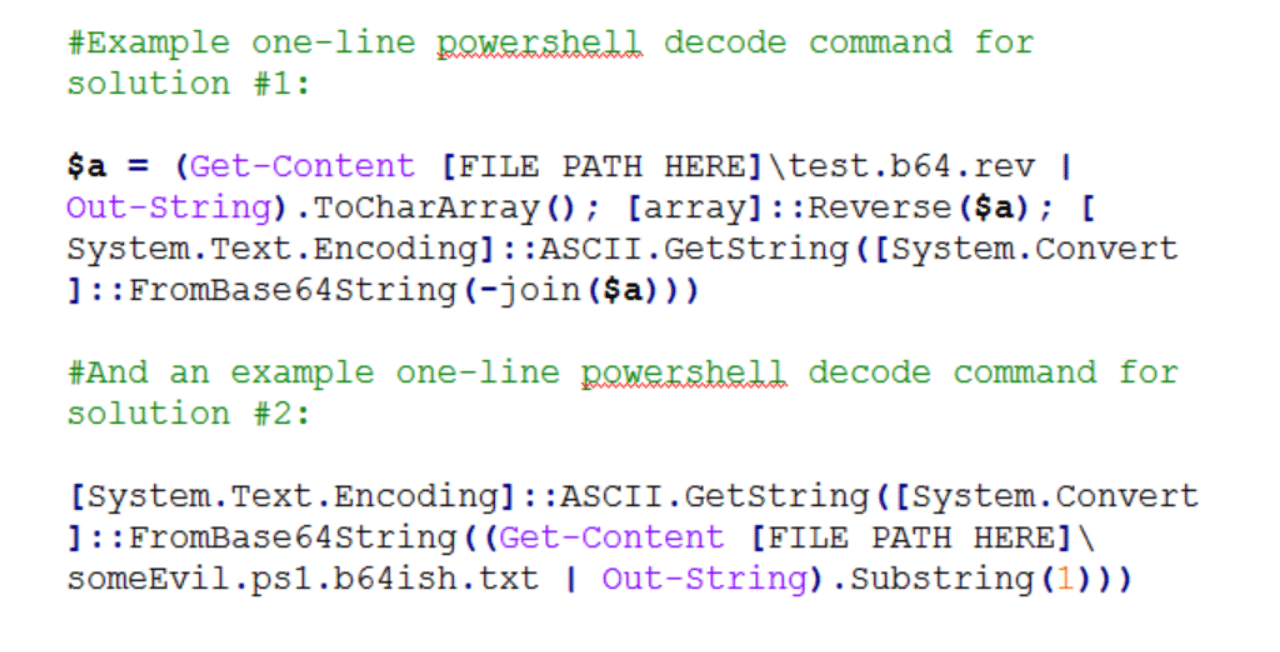
AV Avoidance – Base64’ish Obfuscation
Here’s a quick and simple anti-virus avoidance trick for malicious payloads. Background I came across the need today to avoid static/string based detection in a suite of AV products for a few powershell scripts I was staging to a box. Typically, I’d use some combination of encryption or custom, semi-complex obfuscation to get past proxy […]
Hacker’s Ethics – My Changing Perspective
Personal Ethics is not something that changes too dramatically over time. The foundation of our ethics is typically laid as children with small changes throughout our life. Untypical, then, was a major shift in my personal ethics as it relates to “security research”, aka hacking. Intro Has your spouse ever told you something a million […]
History of the Term EDR
Today I asked myself, When did the term EDR come out? It seemed to just come out of left field. What is EDR? EDR = Endpoint Detection & Response: “This name reflects the endpoint (as opposed to the network), threats (as opposed to just malware and officially declared incidents), and tools’ primary usage for both detection and […]