I recently had the privilege to perform full scope application security testing against 1E’s Tachyon, an endpoint incident response and remediation platform. I was so impressed with it, I sought (and received) approval from 1E to release this article publicly, detailing my impressions. Earlier this year, 1E and I began dialoguing about the possibility of evaluating […]
Month: September 2018
Binary File Patching – Echo Command
Here is a single line Windows batch command which renames and patches a binary in order to avoid detection. The Problem Many detections that look for malicious or uncommon usage of built-in Windows tools/utilities (i.e. attackers living-of-the-land) depend on well-known file/process names (ex. powershell.exe). But, if defenders are also monitoring for the well known checksums […]

Burp+SSLintercept with Kali+Docker+Java+Python+Browser
I couldn’t find a single source for setting this up, so I thought I would copy/paste my notes for others to reference. Feedback appreciated. The goal is to proxy all http-80 and https-443 traffic in a docker/OS stack through Burp with (trusted) SSL intercept. My Environment: Notes: The Steps – Host OS: Install Burp from […]
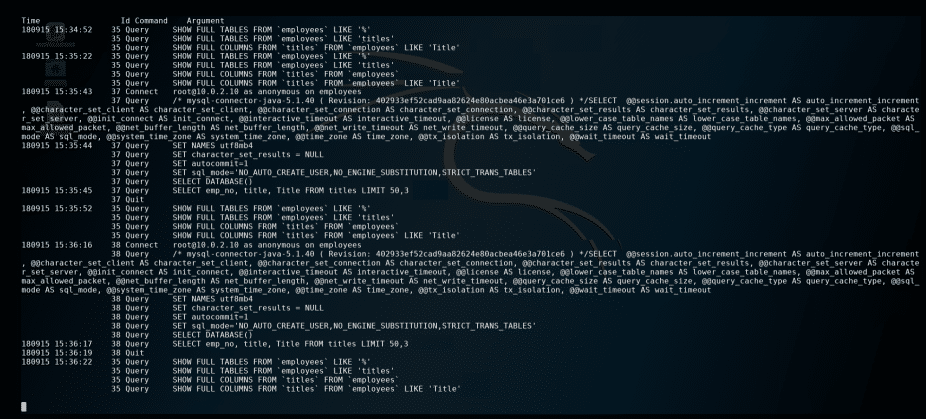
Passwords in DB Logs
This was useful (for an attacker) when password hashing (during authentication) was being performed at the DB level. Background Having access to a DB with encrypted (and salted) password hashes can still present a challenge to recovering a significant percentage of the cleartext passwords. Sure, one will be able to crack some using a decent […]
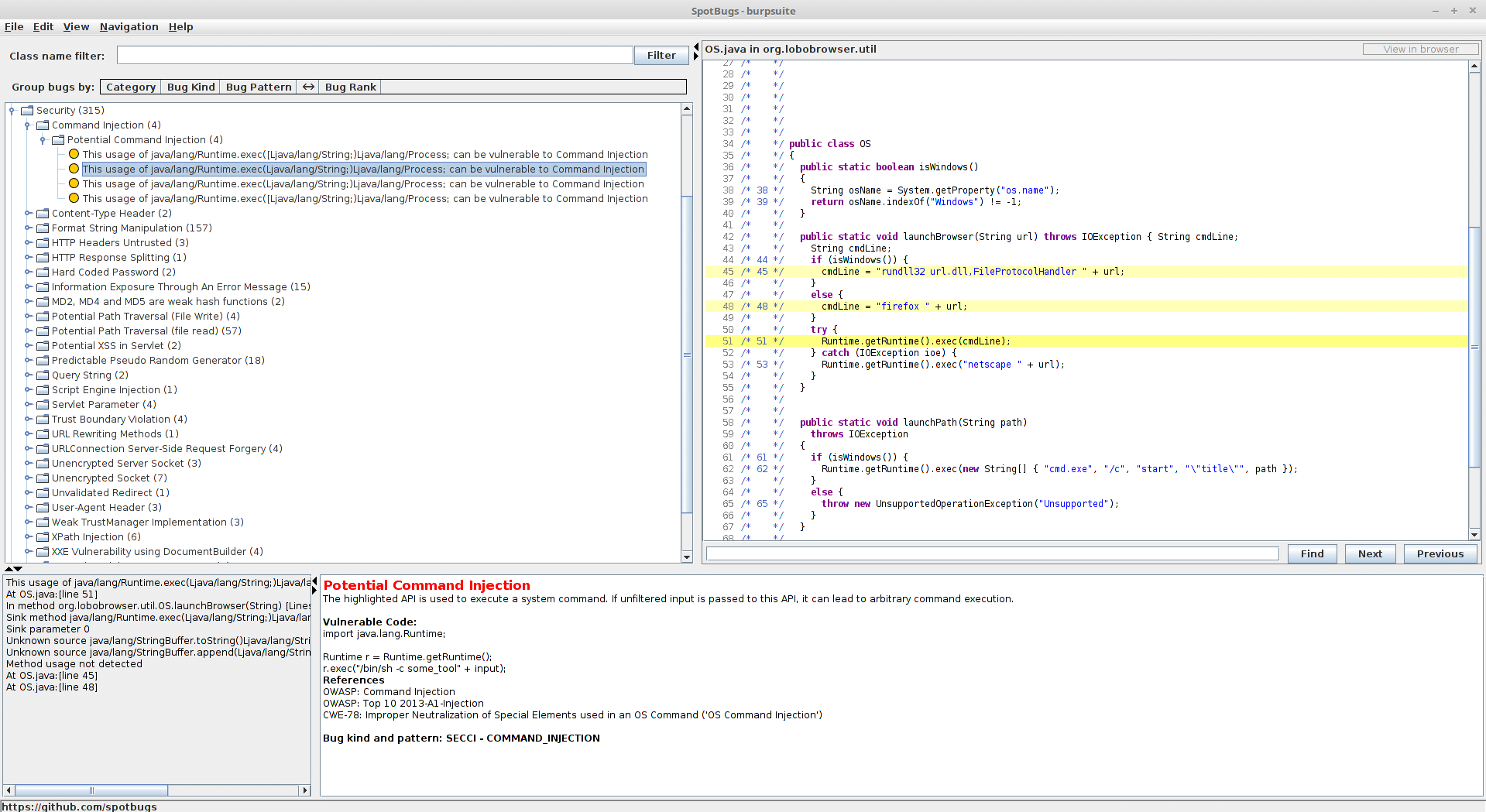
Finding Vulns in JARs with Spotbugs
How to find security vulnerabilities in JARs with SpotBugs… [Note: burpsuite is just being used as an example] Spotbugs is awesome. But, the instructions for compiling it and running as a standalone app were not that clear to me. Because of this, I decided to put together the rather simple steps below. Prerequisites Decompile the […]

