How confident are you that visitors within your organization are constantly supervised by an employee? How often does an employee fail to properly hand off their escort duties to another employee? This is a solution we came up in response to a recent physical Social Engineering Assessment we preformed for a client. It is an all too […]
Year: 2019
Selecting a Reputable Security Testing Company
When choosing a security testing company to perform penetration testing, red teaming, etc., there are a few things you should consider to guarantee that you find the optimal company for your situation. Transparency: If you can’t answer all, or nearly all, of the following from the company’s website, they are not transparent. Company Size: Size […]

Vendor: Protect Your Code and Your Customers
Security through obscurity is no security at all. Obscurity does indeed add an extra level of protection and should not be ignored altogether. When creating an application, a vendor should follow all best practices to protect their application/code from “reverse-engineering, tampering, invasive monitoring, and intrusion” (Source: OWASP.org). OWASP calls this “Application Hardening and Shielding”. Read […]
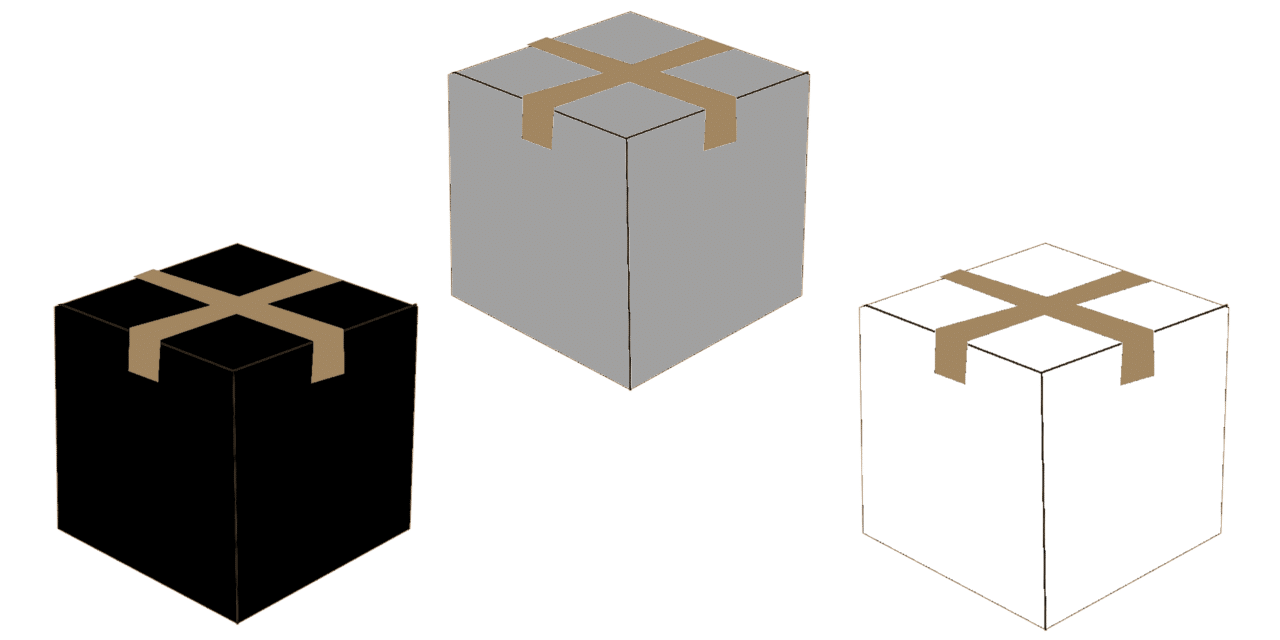
Gray Box vs. Black Box vs. White Box Testing
The balance of white/black box security testing is a decision you will ultimately make based on your budget, risk concerns, internal policies, and possibly compliance requirements. This article is intended to help a client think through the benefits of white box testing and the downsides to full black box testing, as well as provide several […]
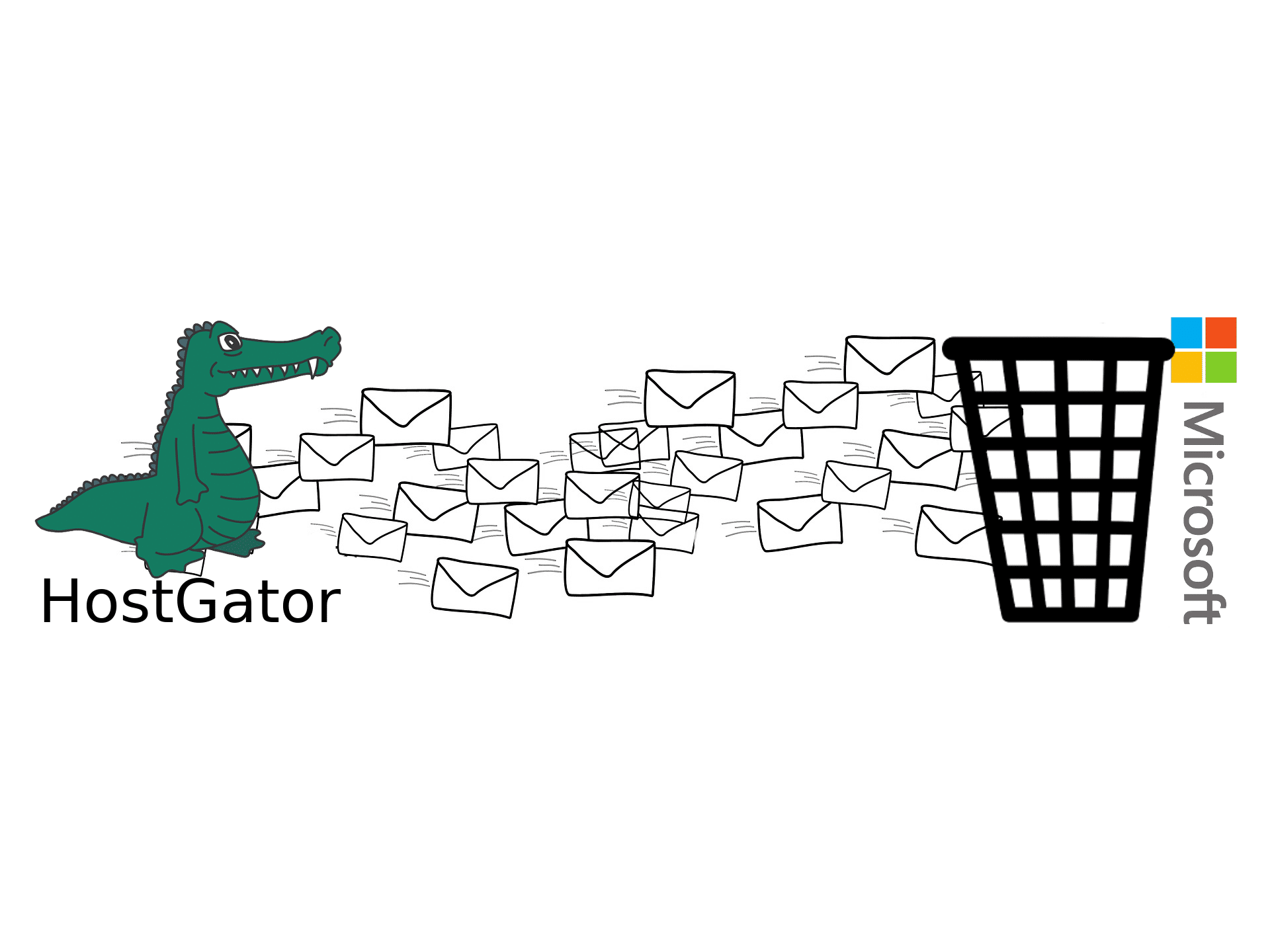
Troublesome: HostGator and Microsoft
This article is to inform you of the incompatibility that exists between HostGator and Microsoft-hosted email services, Microsoft’s inability to accurately distinguish good email from spam, and how unhelpful they both have been in resolving the issue. I hope this article will help inform two groups of people: (1) those currently using/those considering using any […]
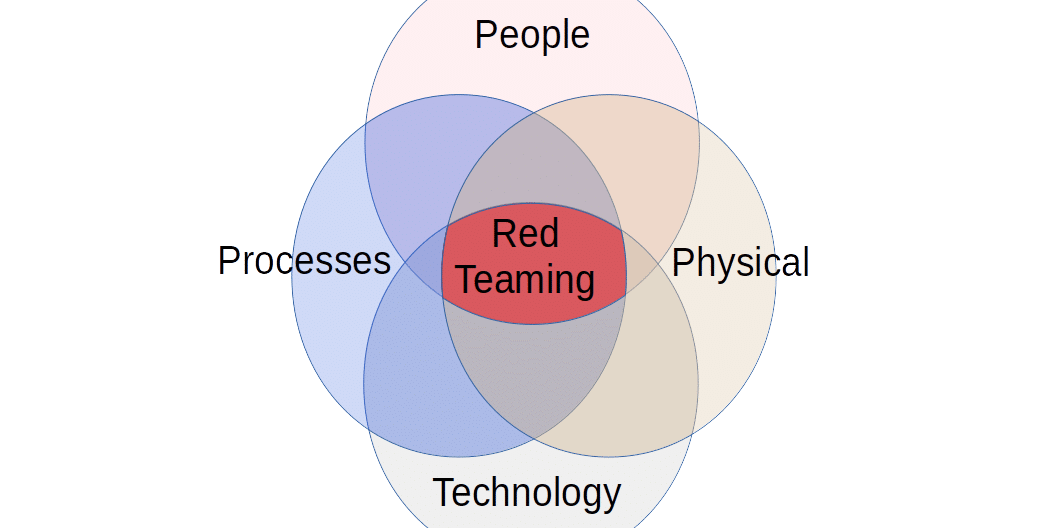
Red Teaming vs Penetration Testing vs Vulnerability Scanning vs Vulnerability Assessments
What is the difference between “Vulnerability Scanning”, “Vulnerability Assessments”, “Penetration Testing”, and “Red Teaming”? What do they mean? Which one do you need performed on your systems? The industry is very opinionated on the definitions of these four terms. This article will share our view of the similarities and differences between vulnerability scanning (vuln scan), […]
Presentation: RATs Without Borders
This presentation, “RATs Without Borders – Moving Your Cheese”, was presented on 29 March 2019 at BSidesATX. Slides: BSides_ATX_2019.pdf Gitlab: https://gitlab.com/J35u5633k/RATsWithoutBorders_public Video recording: https://www.youtube.com/watch?v=ZubIQfHEUzA Original event details: https://bsidesaustin2019.sched.com/event/M5yt/rats-without-borders-moving-your-cheese Description: Antivirus solutions continue to fail us. This talk will highlight my research on the effectiveness of the leading AV solutions. The overall strategy is to create a RAT in every […]

Threat Intelligence and Brand Monitoring
One thing that nearly every department in your organization is concerned with is monitoring for references to your organization on the internet, such as brand reputation, cybersecurity threats, intellectual property rights, threats of harm against life or property, etc. But, what are your options? [This is a work in progress in which we intend to […]
A Sensible Password Policy
A password should be 24+ characters, require lowercase, uppercase, numbers, special characters, not one of the last 24 passwords, not more than three characters in a row of the same type, and change every 30 days. Uh, NOT! Here’s a more sensible policy. The policy described in the intro is a real policy in some […]

